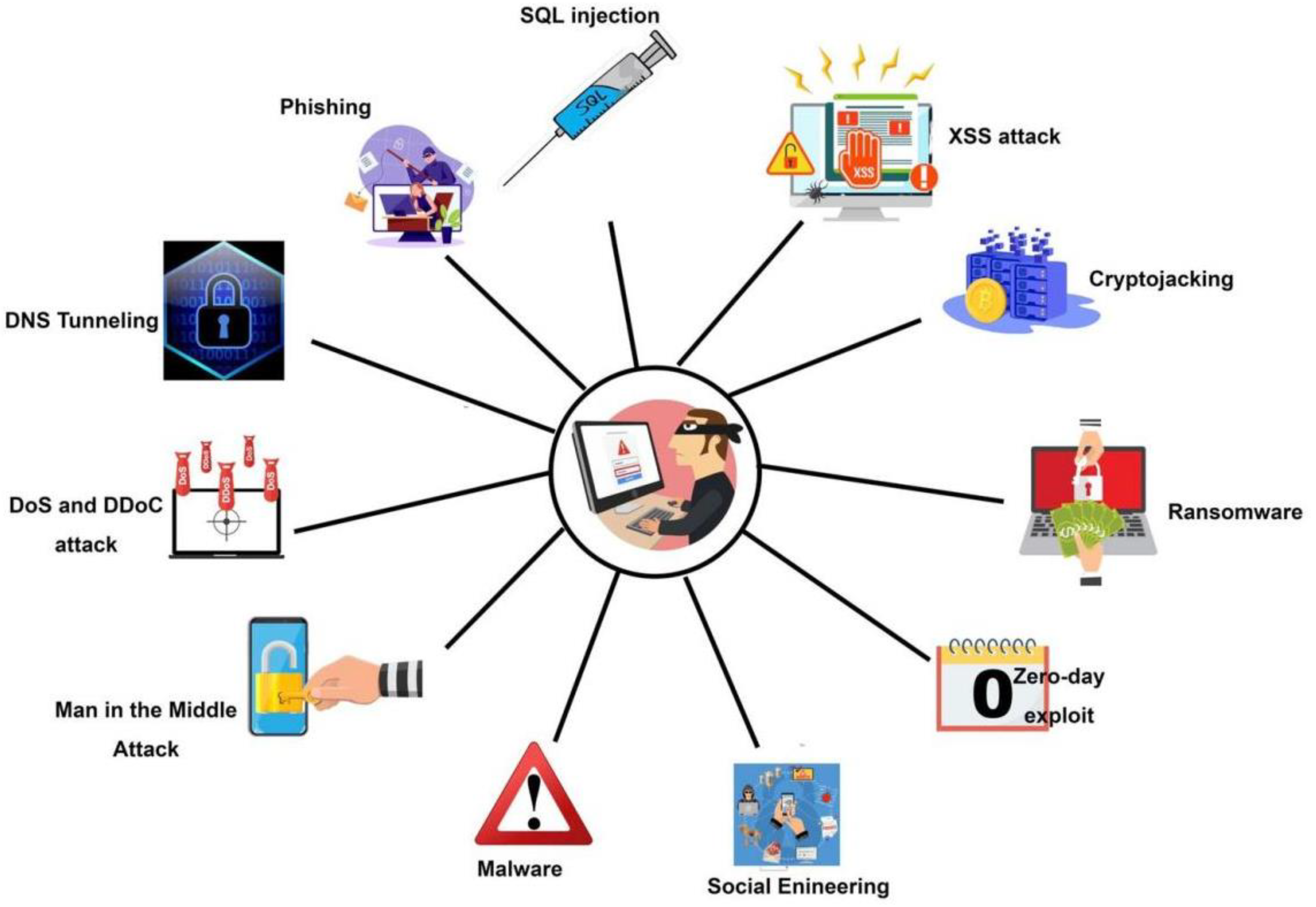
Malware analysis Malicious activity
4.6
$ 37.50
In stock
(757)
Product Description

2: Block diagram of malware detection and classification system

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog
Symmetry, Free Full-Text

7 Benefits Of Dynamic Malware Analysis
Malware Detection: 7 Methods and Security Solutions that Use Them

Malware Analysis: Steps & Examples - CrowdStrike

Malware Analysis — Part 1. Malware, as the name indicates is…, by Akash Sarode

Behavior-based malware analysis process as conducted by our
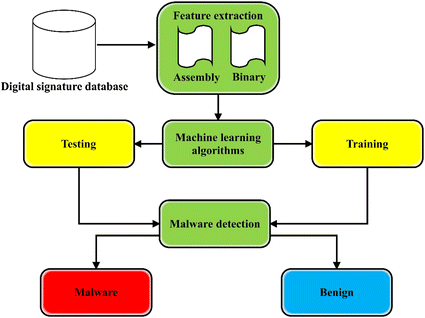
A state-of-the-art survey of malware detection approaches using data mining techniques, Human-centric Computing and Information Sciences

Malware Analysis: Tips, Tools, and Techniques

How to Do Malware Analysis?

Top 10 Malware Analysis Platforms & Tools